10 May 2019
The Federal Bureau of Investigation (FBI) and Department of Homeland Security (DHS) have issued a joint Malware Analysis Report (AR19-129A) on a new malware variant used by the North Korean government. This malware was detected while tracking the malicious activities of the North Korean-backed hacking group Hidden Cobra (also known as Lazarus) and has been identified as Electricfish. Lazarus Group is a cybercrime group made up of an unknown number of individuals. While not much is known about the Lazarus Group, researchers have attributed many cyberattacks to them over the last decade. A notable attack by the group is the attack on Sony Pictures in 2014, which was the start to one of the largest corporate breaches in recent history. The hackers were able to cripple the Sony network for several days and gain access to valuable insider information including previously unreleased films and the personal information of approximately 4,000 past and present employees. The group was also able to access internal emails and reveal some very speculative practices going on at Sony. This latest report on Electricfish, published on the US-CERT website, comes with a detailed analysis of one malicious 32-bit executable file found to be infected with Lazarus' Electricfish malware. In this file, the malware appears to implement a custom protocol that creates a connection between the infected host and an external, malicious, destination host, bypassing authentication controls to reach outside of the network.
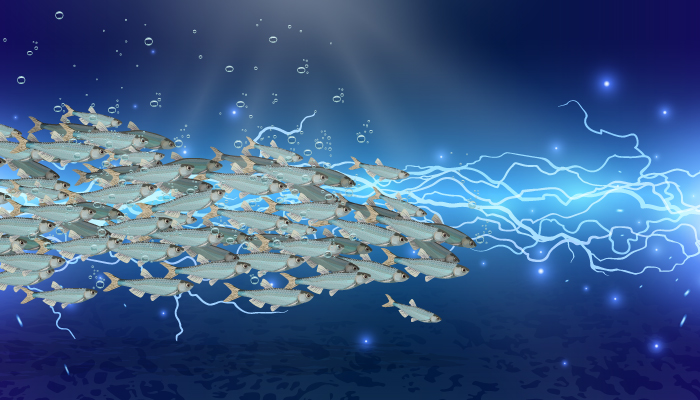
Once a connection has been established, the Electricfish malware is able to funnel internet traffic between the two machines allowing the malicious actors to funnel information collected from compromised computers to servers that they control.
The full, detailed report and analysis for the Electricfish malware sample as well as a full list of Indicators of Compromise (IoC’s) are available within the AR19-129A advisory.